Today I am talking about DNS spoofing and DNS
Spoofing is an attack where a person forges fake DNS Responds to trick a victim
computer into accessing a different website. Whenever you visit a website such
as www.infinityexists.com the domain name is translated to the IP address of
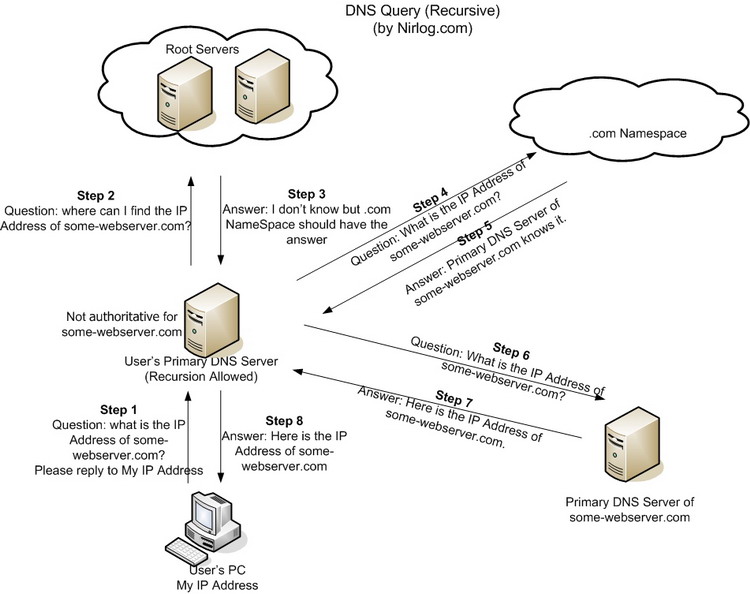
the web server. To do this your computer makes a DNS request to a DNS Server,
and the server returns a DNS Respond which contains the IP address of the web
server. Therefore, during a DNS Spoofing attack the victim computer receives an
Spoofed IP address and attempts to connect to that web server. However, often
times a web server hosts multiple website by utilizing Virtual Hosting. Virtual
hosting is a method that allows a web server to host more than one domain name
on the same computer and the same IP address. If an Attacker wants to DNS Spoof
a website which is a virtual host on a web server the IP address is not
sufficient information for the web server to determine which website the victim
computer wants to access. Therefore, the DNS Spoofing attack will not work correct.
The way a web server determines which website a person wants to access is with
the Host Header contained in the Get Request. Consequently, an Attack needs to
modify the victim’s Get Request to have the correct Host Header before it reach
the web server. To do this I combined an Ettercap Filter that will Log and Drop
the Get Requests from the victim, and a C program which will change the Host
Header. After the Host Header is modified, the Ettercap Filter submits the new
Get Request to the web server. This process will allow an attacker to perform
DNS Spoofing attack with a Virtual Host.

No comments:
Post a Comment